Best Information Security Practices in 2024: Essential Checklist for CSOs
Key Takeaways
- Phishing-Resistant MFA
- E2E Encryption
- Shadow IT Control
Need Expert Advice?
Our experts are ready to help you secure and evolve your infrastructure with the latest technologies and custom solutions.
Contact Us TodayIn 2024, security is no longer just the responsibility of the IT department; it's a core business risk management function. With ransomware becoming more sophisticated, organizations must move beyond basic firewalls and adopt a multi-layered security strategy that protects data, identities, and infrastructure.
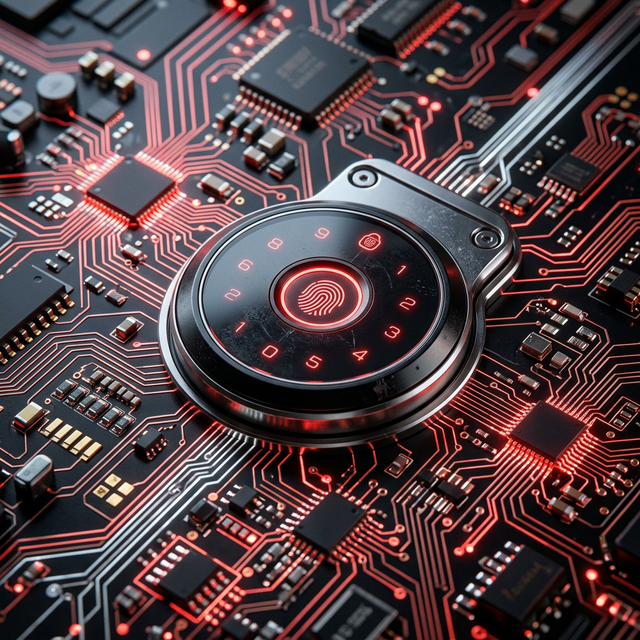
1. Advanced Identity and Access Management (IAM)
Password-based security is effectively dead. 2024 calls for phishing-resistant multi-factor authentication (MFA), biometric verification, and just-in-time access privileges. Managing who has access to what, and under what conditions, is the first line of defense.
2. Data Encryption Everywhere
Data must be encrypted not just in transit, but also at rest and during use. Implementing end-to-end encryption across all communication channels and storage systems ensures that even if a database is breached, the information remains unreadable and useless to the attacker.
Meet Our NexBot AI
Get instant answers about our services, infrastructure solutions, and technology.